AML/CTF Reforms and Privacy
Australia’s updated anti-money laundering and counter-terrorism financing laws will reshape compliance obligations for many businesses, particularly those brought under the regime for the first time. But there is another effect worth noting: once a business becomes an AML/CTF reporting entity, the Privacy Act 1988 (Cth) (Privacy Act) will cover it as well. For many small firms across the Tranche 2 professions, 1 July 2026 will mark their first encounter with Australia’s privacy laws.
Why reporting entities must pay attention to privacy
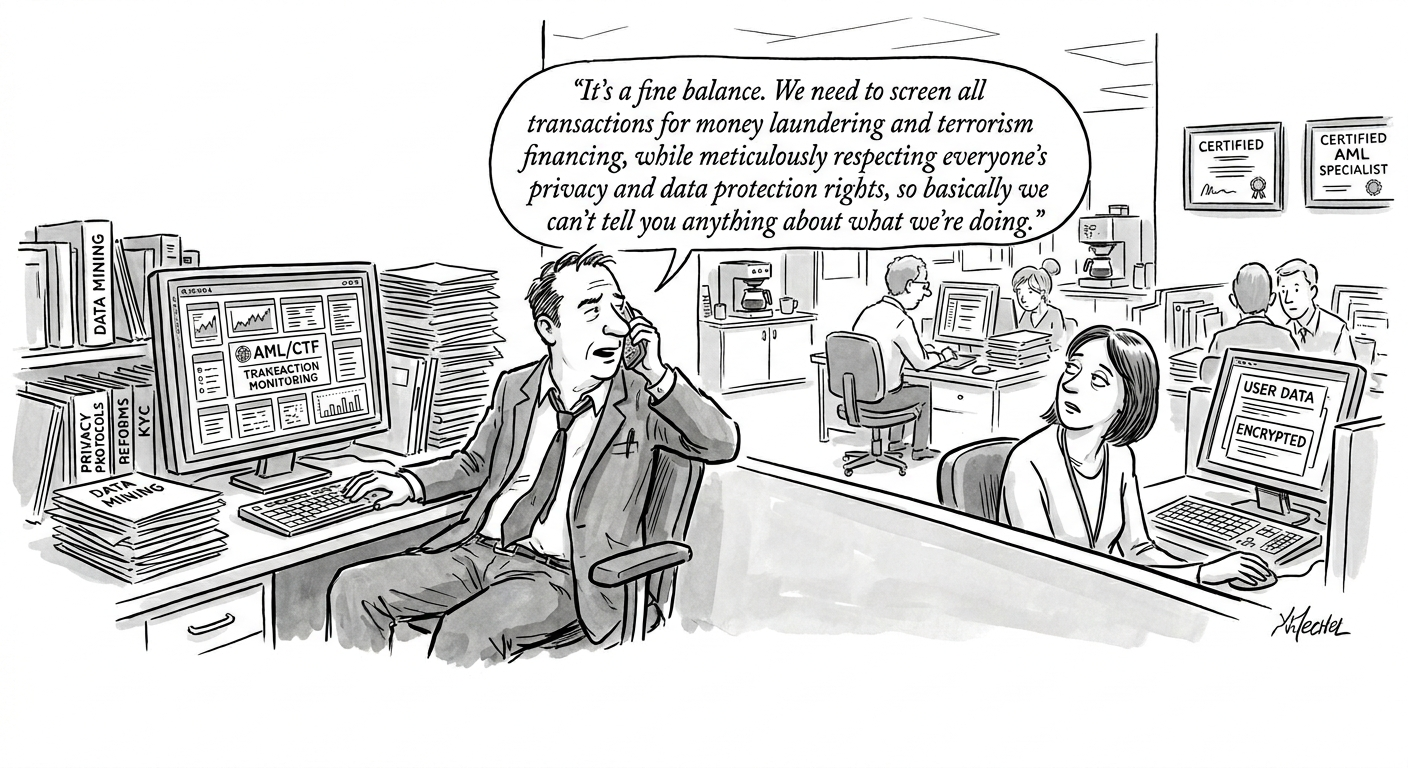
While the AML/CTF framework and the Australian Privacy Principles (APPs) can look like competing regimes, in practice they must operate together. Virtually everything a reporting entity does in that capacity — collecting identifying information, running verification checks, monitoring transactions and escalating suspicious matters — involves personal information. Understanding where the two frameworks meet is now a basic governance requirement.
How the Privacy Act applies
The Privacy Act covers every AML/CTF reporting entity, regardless of whether the small business operator exemption would otherwise exclude it. That exemption turns on annual turnover: under $3 million. Once a business becomes a reporting entity, the exemption falls away.
However, for a small business operator that is a reporting entity, the Privacy Act only extends to activities carried on for the purpose of, or in connection with, compliance under the Anti-Money Laundering and Counter-Terrorism Financing Act 2006 (Cth) (the AML/CTF Act) or regulations made under it. Authorised agents of a small business operator that is a reporting entity are treated the same way.
In practice, the volume and variety of personal information involved in AML/CTF compliance means it will often be difficult for a small business operator or its authorised agent to cleanly separate AML/CTF activities from the rest of the business when complying with the Privacy Act.
OAIC guidance
The Office of the Australian Information Commissioner (OAIC) is the privacy regulator. It published guidance for AML/CTF reporting entities in February 2026, and then quickly updated the guidance in April 2026.
The updated guidance offers some reassurance about the regulator’s approach. The OAIC takes a risk-based, harm-focused stance, directing its attention to conduct most likely to cause real harm. It also acknowledges that compliance may require significant changes to systems and processes, and that getting there will take time. Businesses making a genuine effort to comply can take some comfort: the focus is on proportionate regulation, not penalties for their own sake.
Entities that are new to privacy regulation, or dusting off existing systems, are encouraged to use the OAIC’s Privacy Foundations self-assessment tool to assess how well their practices, procedures and systems hold up. The message is practical: identify gaps early, get the basics right, and have a workable privacy management plan in place before the new obligations land.
The guidance includes a privacy essentials checklist for reporting entities. The OAIC has also prepared a collection notice template which is available on its website.
Authorised agents of reporting entities should not assume that privacy compliance is solely the reporting entity’s concern. Where an agent handles personal information for AML/CTF purposes, it too must have workable privacy processes in place for those activities.
Privacy policies and notices
Every APP entity must maintain a clear, current privacy policy. For reporting entities, that policy should expressly address how personal information is handled for AML/CTF purposes — covering the collection and use of identifying data, financial information, risk assessments and reports to AUSTRAC.
Collection notices are equally important. The APPs require organisations to tell individuals what is being collected and why. Where the collection is required by an Australian law, the entity must name it. AML/CTF‑driven customer due diligence therefore needs to be identified as such in the collection notice.
There will be cases where giving notice would cut across the AML/CTF tipping-off rules. In those situations the better course is not to over-explain, but to draft notices that are clear where they can be, and appropriately limited where the law demands it.
Collecting only what is reasonably necessary
Under the APPs, organisations may only collect personal information that is “reasonably necessary” for their functions and activities. For reporting entities, AML/CTF obligations are clearly part of those functions. Information prescribed by the AML/CTF Act or Rules — identity data, beneficial ownership, or politically exposed person (PEP) indicators — will generally meet that test. But businesses should still ask whether additional, non‑prescribed data is truly essential, or whether they are gathering more than the job requires.
Small data minimisation oversights can compound into material privacy risk, particularly where sensitive information is involved. PEP screening, for instance, may capture political or criminal history — “sensitive information” under the Privacy Act. The AML/CTF Act authorises that collection, but policies should say so clearly.
The OAIC guidance also flags the source of collection. Personal information should generally come directly from the individual, unless that is unreasonable or not practical. AML/CTF work will create exceptions — for instance, collecting beneficial ownership details from a customer rather than the beneficial owner — but those departures should be deliberate and tied to a specific compliance need.
Biometric information is also sensitive information. Consent should generally be obtained before using biometric checks for customer verification. Businesses considering these tools should ask whether they are truly necessary, ensure individuals are clearly told what will happen to their data, and offer an alternative verification path where possible.
Using and disclosing AML/CTF information
Personal information collected for AML/CTF purposes must generally be used only for those purposes, subject to exceptions. The most significant is the APPs’ permission to use or disclose where “required or authorised by law” — which extends to suspicious matter reports, threshold transaction reports and responses to AUSTRAC notices.
A specific authorisation also permits the use of credit reporting bodies for identity verification, though improper use of that mechanism is treated as an interference with privacy.
Outsourcing compliance functions does not outsource accountability. Where reporting entities engage third‑party service providers, contracts must set clear standards for privacy compliance, information security and breach notification. Before signing up a provider, businesses should do some basic due diligence on how it handles personal information — its security controls, breach response capability, retention settings and whether data may be held offshore.
Overseas disclosure, data quality and data security
AML/CTF compliance will sometimes involve sending personal information overseas. APP 8 ordinarily requires organisations to ensure foreign recipients do not breach the APPs, but that requirement does not apply where an Australian law authorises the disclosure. Even so, international AML/CTF disclosures should be kept strictly within what the law permits.
Given the sensitivity of AML/CTF data, APP 11’s reasonable security obligation carries real weight here. Policies should address encryption, access controls, segregation of duties, audit logging and other protections proportionate to the risk. Entities are also expected to maintain a data breach response plan, which should be integrated with AML/CTF processes.
A data breach response plan must also account for AML/CTF secrecy obligations. In some circumstances, an eligible data breach will need to be reported to the OAIC but not to the affected individual, where doing so would conflict with secrecy provisions or tipping-off restrictions.
Access, correction and record retention
Individuals ordinarily have a right to access their personal information, but AML/CTF creates several exceptions. Access may be refused where it would breach the tipping‑off prohibition, prejudice an enforcement activity, or cut across another Australian law. Any refusal must be documented.
In some cases a business may not be able to say much about a refusal at all. Where explaining the reasons would itself risk tipping off the individual or cutting across the AML/CTF regime, a limited response is acceptable. What matters is having a consistent process for fielding those requests and escalating them appropriately.
Both the AML/CTF Act and the APPs require information to be kept accurate and current. These obligations generally pull in the same direction: keeping records up to date for Privacy Act purposes will usually also satisfy ongoing customer due diligence requirements.
Record retention is a further point where the two regimes overlap. The AML/CTF Act prescribes a seven-year retention period for certain records. APP 11.2 would ordinarily require personal information to be destroyed or de-identified once no longer needed, but that requirement gives way where an Australian law demands retention. Once the AML/CTF period expires, however, the business should revisit whether holding on to the information is still justified.
One particularly practical point concerns identity document copies. Under the updated AML/CTF framework, businesses generally do not need to retain full scanned copies of passports or licences just to meet their record-keeping obligations. In most cases, recording the relevant details from the document and noting what was checked will be enough. Where full copies are no longer needed, they should be destroyed or de-identified.
The OAIC acknowledges that unwinding older ID document retention practices may take time. Businesses are expected to be actively moving toward the new position, supported by a documented plan, management oversight and interim safeguards while legacy holdings are dealt with.
Where to from here?
For many organisations, particularly smaller professional services firms, the privacy dimension of joining the AML/CTF regime is only now registering. The systems, notices, policies and contracts built for AML/CTF compliance cannot be siloed from the Privacy Act; they need to work together from the outset.
Privacy compliance is not an add-on to AML/CTF. It should be woven into the business’s day-to-day controls, risk management and governance from the start.
If you would like assistance preparing for AML/CTF or privacy compliance, please get in touch.